Security in the crypto world in 2026 is particularly relevant. It is no secret that digital assets long ago ceased to be something "geeky" and far removed from the everyday life of the average person. In many countries, crypto is already actively used not only to participate in complex earning schemes, but also to carry out simple tasks.
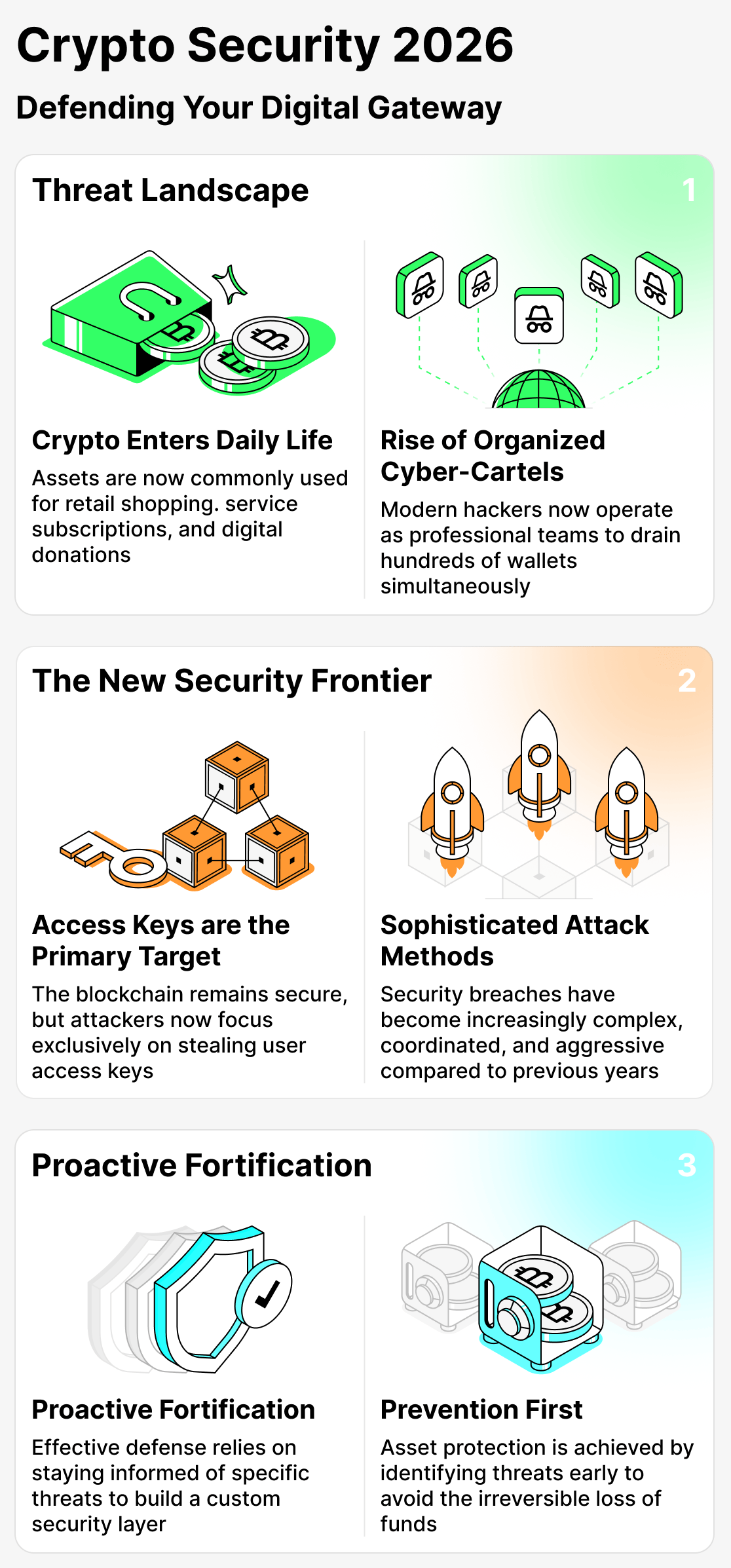
For example, more and more people now use cryptocurrency to pay for subscriptions to various services, send donations, and even make purchases at some stores.
But behind this rapid development of the crypto industry lies an unpleasant side. Along with the spread of digital assets, the number of cyberattacks resulting in the theft of users' funds has increased. Furthermore, it's not just that there are more attacks — they have become more sophisticated, more complex, and more aggressive.
Modern hackers are increasingly unlikely to work alone. More and more often, entire teams of attackers are emptying the wallets of dozens, even hundreds, of ordinary people!
The trend is that it is not the blockchain itself that is under threat, but the access keys of asset holders.
That's why it's important to pay special attention to security and keep your finger on the pulse. After all, if you know what might threaten you, you can prepare and do everything possible to prevent losing funds.
In this article, we will not only examine the most pressing threats in the crypto world, but also offer practical tips to help you build effective defenses and avoid the unpleasant and unexpected consequences of encountering attackers.
Major threats in crypto in 2026: how users lose money
Hackers actively exploit users' trust and inexperience.
Imagine: you've just started getting into cryptocurrencies, installed your first wallet and maybe even managed to buy some assets. Then a 'support specialist' from an exchange messages you and asks you to hand over your access keys, saying that 'your funds are at risk.' You trust them, do what they ask, and instantly lose everything!
That's why you should take security especially seriously when it comes to money.
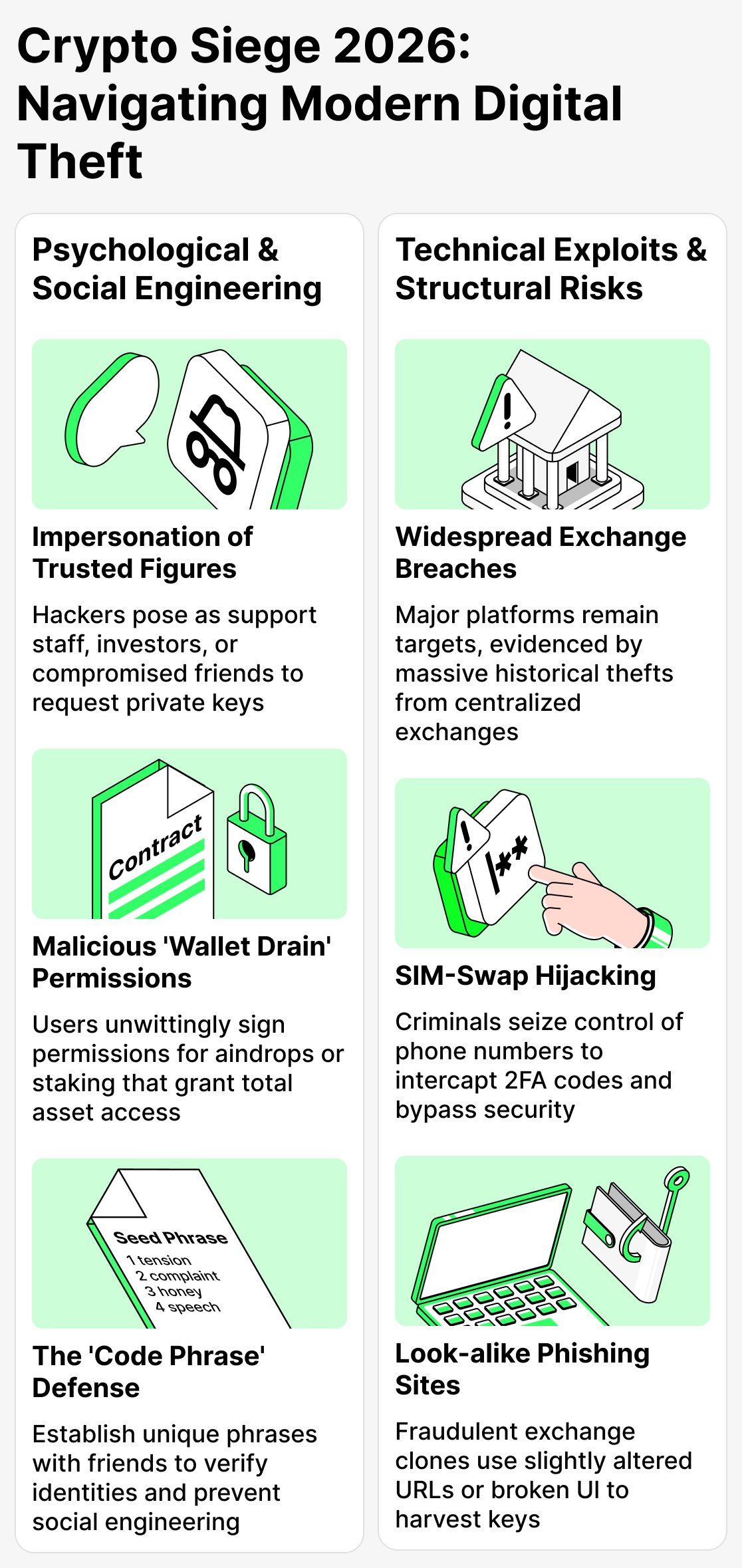
Social engineering and scams
Scammers are increasingly resorting to psychological tricks to gain your trust. They prey on your fear and lack of experience. Today hackers often pose as support managers, investors, and community administrators.
They can also speak on behalf of your friends and acquaintances! To do this, they first hack users' social media accounts and then use them to find potential victims. So another conversation with your best friend can turn into the loss of all your crypto holdings!
Be extremely careful. Better yet, prepare a "code phrase" for each. It may sound a bit radical, but it will make you harder to deceive.
Wallet drain and theft via approvals
This is also a very common scheme. A user is offered an airdrop (to take part in a crypto giveaway), to participate in staking, or simply to "check their wallet." They are asked to sign a transaction with their private key, but instead they sign a permission granting access to their assets.
Hackers can skillfully disguise transactions, so an ordinary user is unlikely to immediately distinguish a fake transaction from a genuine one.
This is how attackers gain access to funds. They usually don't withdraw crypto immediately to avoid arousing suspicion; they typically do so after some time.
From the blockchain's point of view, such an operation looks legal. After all, the user themselves gave the scammers access to their assets. Therefore a hacker can simply withdraw your funds if you gave them access, and will most likely face no consequences.
Very important: never give your access keys to anyone and never sign transactions unless you are 100% sure about them!
SIM-swap and account takeover
SIM hijacking has always been a concern. In this way, attackers, long before crypto became popular, gained access to users' data and blackmailed them.
Now a SIM card can become the key to the crypto of an unlucky, careless enthusiast.
If criminals gain access to your phone number, they can receive messages containing passwords, access codes, and other important information. Thus, a fraudster with access to your SIM can take various actions to gain access to your crypto.
The moral: if you see strange messages or codes you didn't request — immediately block your SIM!
Fake websites and address spoofing
Skilled scammers can create duplicates of legitimate services and platforms. If you visit such a site and enter your access key, you will inevitably hand it over to the scammers!
This issue is especially relevant for users of cryptocurrency exchange services. There are so many such platforms that it can be extremely difficult to tell a legitimate service from a fake.
Always pay attention to how the webpage looks. If something seems suspicious (the font is distorted, some buttons aren't working) — don't enter anything there! Look for a more reliable option.
Hacking real services
Even developers of reliable platforms cannot always ensure complete security for their users. Recently, the number of hacks of major exchanges and exchange services has increased.
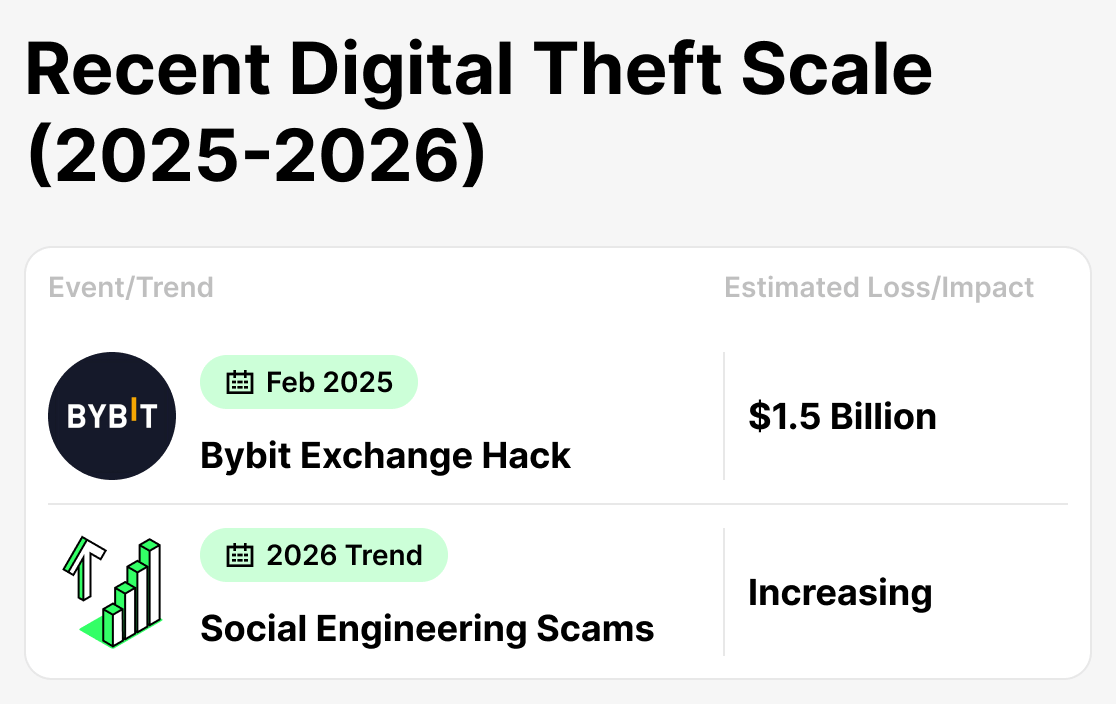
For example, in February 2025 the very popular exchange Bybit was hacked. The attackers managed to steal about $1.5 billion in crypto from users. And that really does happen. Moreover, the success of some hackers motivates others to take action. So with each successful attack, the number of new hacking attempts increases.
How to protect your crypto assets in 2026: three layers of security
We've identified which attacks are most relevant right now. But what should you do about them? Simply hope they'll pass you by? Not at all! There are time-tested rules and protection methods that will always work!
Conventionally, all methods of creating a secure environment for working with crypto can be divided into three layers. Let’s examine each in detail.
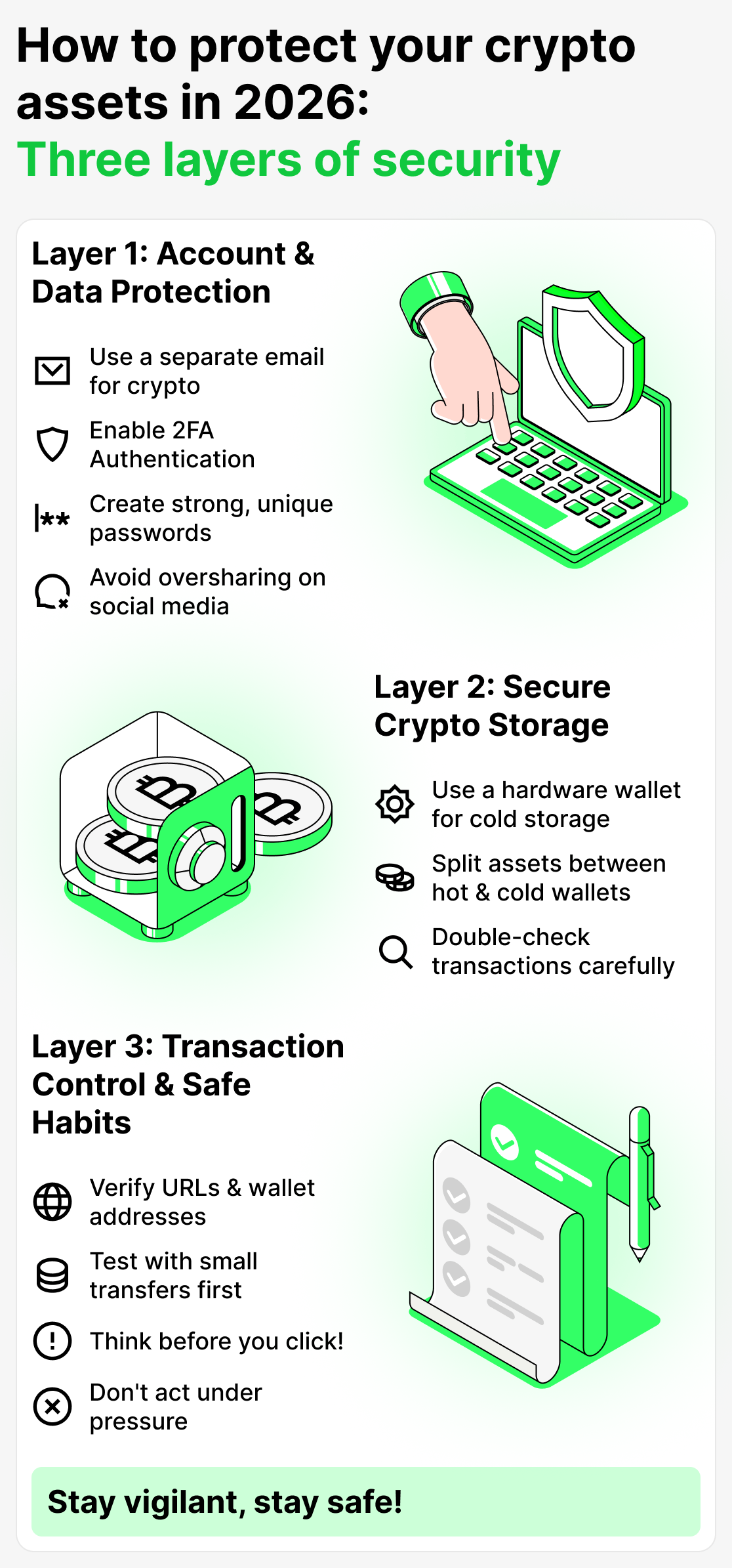
Layer 1 — Account and personal data protection
Your personal data is the foundation. If a scammer gains access to your email or phone number, they will be able to get to your crypto. It will take some time, but criminals usually find a way.
Here's what you absolutely need to do to minimize the risk of third parties gaining access to your data:
- Set up a separate email account for registering with cryptocurrency services. Even if your primary email is hacked, scammers won't be able to access the data you store elsewhere that isn't connected to the compromised account.
- Enable two-factor authentication. This is an additional layer of protection offered by many services. That way, in addition to your password, you'll also be required to enter a code sent via SMS.
- Use strong, unique passwords for each service. The more complex the password — the harder it is to crack. Often people use the same password everywhere. That's a bad idea! If an attacker learns such a password, they could gain access to many of your accounts. Also avoid using passwords like qwerty or 1234567 — those are the first things they'll try to guess.
- Don't share too much about yourself on social media. Sometimes users willingly give scammers all their data. If you actively use cryptocurrency, try not to publicize your life or reveal personal information. This especially applies to “crypto-bloggers” and others who openly talk about their connection to crypto — they often become primary targets.
Layer 2 — Secure storage of crypto assets
Keeping all your assets in one place in 2026 is extremely risky. It's frightening to lose part of your money, but it's far worse to lose everything at once. That's why you should split your assets and use them only for their intended purposes.
It's best to use a hot wallet (connected to the network) for everyday transactions, and a cold wallet (with no internet access) for long-term crypto storage. That's much more secure. You can even create a paper crypto wallet using a dedicated generator. This storage method is generally considered one of the most secure.
And a few more useful tips: never sign a transaction “blindly” and don't connect your wallet to services you're not sure about. Double-check everything first, read customer reviews, and only then send money.
Layer 3 — Transaction control and good habits
And yet the most common cause of losing funds is simple human error. We sometimes rush, overlook certain details, and generally don't think about the consequences. However, all of this can be costly…
The best remedy for this is helpful habits. You'll need to develop and reinforce them, but if you succeed, you'll make mistakes noticeably less often. To begin, simply create a checklist of the things you must do before sending funds:
- Check the website domain. There should be no unfamiliar characters or strange words.
- Verify the recipient's address. If the funds are sent to the wrong address, they are very likely to be lost.
- Make a small test transfer. Don't send everything at once. Verify that the funds successfully reach the recipient. This reduces stress and helps you avoid losing capital in case of an error.
- Don't rush or act under pressure. Scammers often use manipulation and tactics of psychological coercion. When dealing with money, try not to act impulsively or give in to panic. Always verify everything and don't take anyone's word for it.
How Cropty Wallet helps improve the security of crypto assets
Cropty Wallet — a next-generation wallet designed to make the experience of using cryptocurrencies as convenient and secure as possible.
The developers placed particular emphasis on protecting user data.
First of all, it should be said that this is a custodial wallet. This means that the access keys are stored by the service itself, not the user. This way, access to your account will be protected by professionals, which significantly reduces all risks.
This approach is especially valuable in today’s environment, as more and more new scams appear each year.
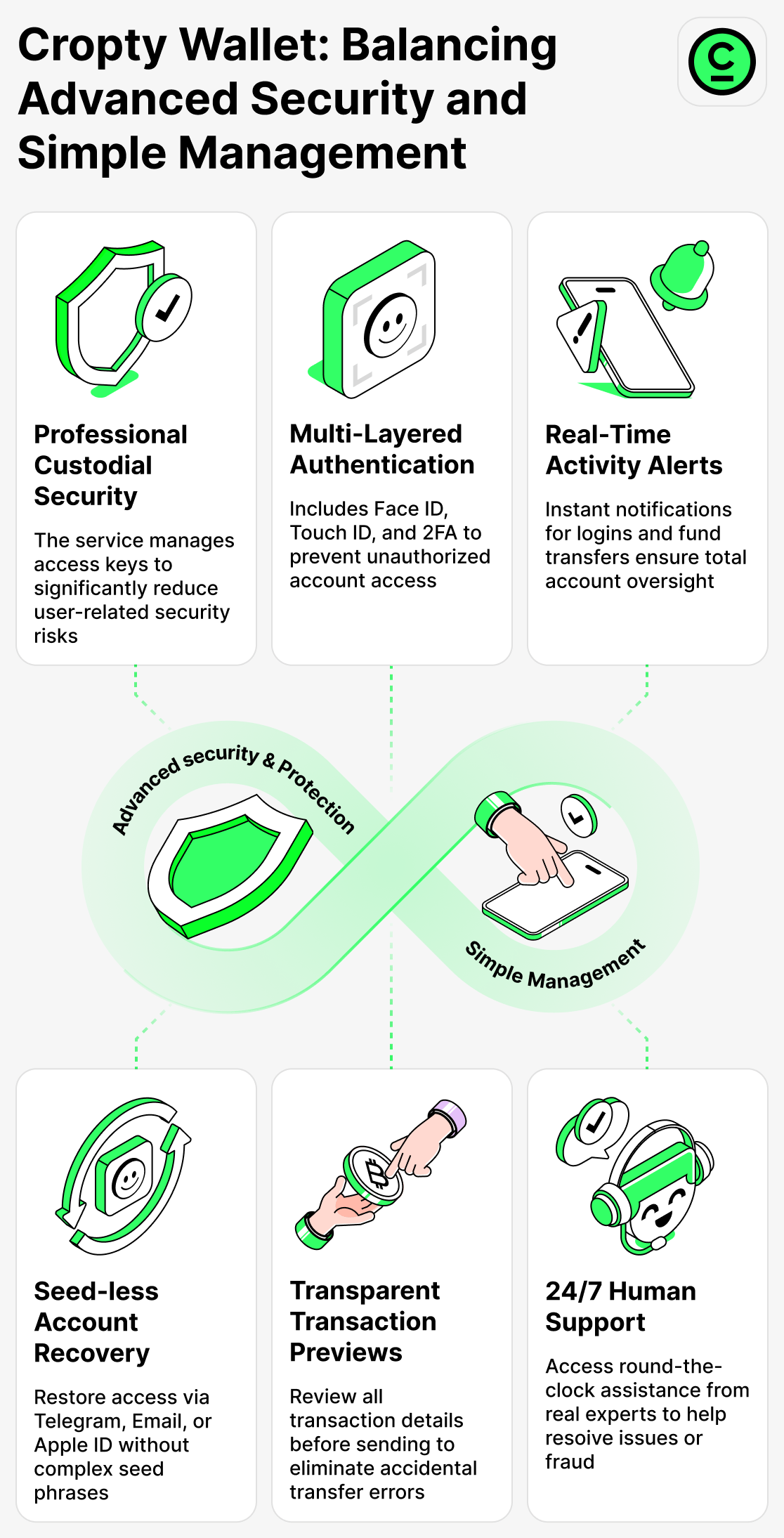
What Cropty Wallet provides in practice:
Secure login and control
You can enable additional layers of protection such as Face ID, Touch ID, and two-factor authentication. In addition, the wallet uses the latest security protocols, which significantly reduce the risk of being hacked.
Transparent transactions
Before each transfer, the user sees all transaction details. This way you can double-check everything, and the likelihood of an error is extremely low.
Easy asset management
The wallet lets you securely store and manage your crypto. You can use this wallet for everyday transactions without worrying that your funds will be at risk. You’ll always receive notifications about key events (sending funds, account login), allowing you to maintain full control.
Simple access recovery
There are no seed phrases or complex recovery mechanisms here. To regain access to your funds, simply use the method you used to register (Telegram, email, or Apple ID).
Caring Customer Support
Cropty Wallet Support is available 24/7. In addition, real people will assist you in your language. If you encounter scammers, specialists will do everything they can to help you. The developers are committed to ensuring the safety of all service users.
In today's environment, those who successfully avoid scammers are not the ones who are afraid of everything, but people who choose reliable services and take responsibility for managing their own capital.
Cropty Wallet is well suited for users who value security and convenience.
How to avoid losing your crypto in the new conditions
The world of cryptocurrencies in 2026 has become faster, more convenient, and more accessible. However, new threats have emerged alongside these advances… In any case, blockchain is rarely to blame when people lose their money. Often, this happens because an individual user is inattentive or unprepared.
But what should you do about all this? How can you protect yourself?
You need to build a system that will guard you against mistakes and protect you from scammers. Develop good habits, stay attentive and take a responsible approach to managing your assets. And when working with crypto, try to choose proven and reliable services.
In 2026, it's not the boldest who win, but the most prepared and attentive.